Industry news
What you need to know about the upcoming price increases for Dynamics 365 products. Introduction Hello all, following the last update around Microsoft Teams, there is […]
Hello and welcome to my Microsoft licensing blog, where I share my insights and tips on Microsoft licensing for businesses. Today I want to talk about […]
Ultima, the AI-powered cloud, security, and digital managed service provider, has today been awarded EMEA Partner of the Year by Kroll, a leading independent provider of […]
Citrix is a leader in providing workspace solutions that enable people to work securely and efficiently from anywhere, using any device. On 4th March 2024 Citrix […]
On December 11, 2023, VMWare officially announced the discontinuation oftheir Perpetual Licenses and SnS Support contract renewals. Going forward, VMWare will exclusively offer subscription licenses for […]
As employees, we play a crucial role in creating a positive impact on the planet, not just within the confines of our workplace, but also in […]
The sharing economy emerges is a new concept that redefines ownership, fosters community, and contributes to a more sustainable future. From car clubs to resource libraries, […]
As the festive season creeps away, you are bored of turkey and the constant repeats on TV. Our focus shifts to the new year and what […]
Hello, it’s Ben here, bringing you a quick 12 essential tips during the festive holiday season. As we get into the holiday spirit and “The 12 […]
I recently received a request to anticipate upcoming technology trends for 2024, set to be featured in our UiQ Edition 5 publication in January of that […]
I was recently asked to make some predictions about technology trends for 2024 which will be released in our UiQ Edition 5 publication in January 2024 […]
While artificial intelligence (AI) has become even more prevalent with the rise of large language models and computer vision capabilities, the question that is often asked […]
Hi everyone! Chris here from the Ultima Labs team. We’re pleased to announce that we’ve hit a new major release milestone with our IA-Connect product for […]
Ultima, a new generation AI powered managed services provider across Cloud, Security and Digital Workspace has announced the establishment of a new office in South Africa. […]
Ultima, a new generation AI powered managed services provider across Cloud, Security and Digital Workspace announces the appointment of Andre Prins as Country Manager for Ultima, […]
QR codes have revolutionised the way we engage with technology, streamlining a lot of processes that were once thought to be a faff. Whether it be […]
In today’s digital landscape, robust cybersecurity is no longer a luxury but a necessity for organisations across all industries. With cyber threats becoming more sophisticated and […]
Microsoft Inspire 2023 was held between July 17th to July 20th and these are the main updates from a Microsoft licensing, products and commercial stance. A […]
There have been many exciting new features and announcements with v12. Here are three things I love with the new release, what are your thoughts? 1) […]
Those who have cybersecurity insurance should investigate the details of cover and terms against cyber breeches and ransomware attacks. Strict conditions and rule changes are speculated […]
As the world faces growing sustainability challenges, businesses are under increasing pressure to rethink their technology strategies in order to support their sustainability goals. In this […]
Endpoint detection and response (EDR) is a critical component of any cyber security strategy. It involves continuously monitoring your network and endpoint devices for signs of […]
In today’s digital landscape, businesses of all sizes are turning to cloud computing as a way to increase efficiency, reduce costs, and scale their operations. While […]
We’re all having to do more with less, at the same time as trying to nurture our employees to prevent talent leakage. So how can automation […]
Successful businesses create a culture that places a positive employee experience at the heart of their workspace strategy. They attract the best talent and deliver a […]
As hyperconverged infrastructure (HCI) continues to mature, living up to its undoubted transformative potential, companies of all sizes are considering how best to use it to […]
Microsoft Azure provides the API App as part of its App Service offering. This supports companies or individuals exposing data and business processes over the web as an […]
Is there anything in the world more dull than Magnolia Paint…. The answer is yes, yes there is, Patching, yet it keeps many of us up […]
Why do we still need Citrix when Azure Virtual Desktop is “free”? There are many potential answers to this, and most will depend on your particular […]
All reputable Buzzword Bingo cards will have entries for “Cloud”, “CI/CD” and “DevOps” on them, and here we will be using all with astounding frequency. I […]
At Ultima, we strive to be an inclusive community along with the support of our valuable workers. Our talented employees operate in close partnerships with businesses […]
Today, the disconnect between business expectation and IT delivery is wider than ever. In this blog, we’ll look at why the technology that enables your business […]
The most targeted platform in the world demands the best email security. The challenge Email is the most universal communication tool for businesses and more than […]
With the increasing threat of climate change, it’s never been more important to do everything we can to work towards a more sustainable future. However, it […]
On Monday 2nd August, Microsoft made Windows 365 Generally Available, bringing around the next iteration of Microsoft’s vision for delivering Windows from the cloud. Windows 365 has […]
When we think back to the start of 2020 when we had to almost restructure our businesses overnight, the main thing which comes to mind is […]
Whether caused by malicious code deployed by sophisticated cybercriminals, weak passwords or simply user error, security breaches are on the rise and threatening businesses across the […]
Escalating demands for high performance and seamless connectivity in any location and on any device have driven a transformation of the modern workplace. However, these increasing […]
As organisations approach the end of the vendor warranty on business-critical IT hardware, they may choose to consider using third party maintenance provision from the established […]
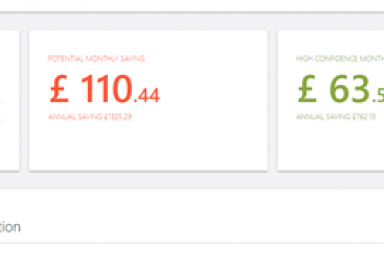
One piece of feedback we’ve had over time is while the advanced optimisation tool is a great feature, it would be even better if cost analysis […]
86 percent of employees believe that a lack of collaboration in the workplace can lead to workplace failures. Have you experienced the same? Collaboration quite simply […]
Computers, technology and software make the modern world go around – but for every piece of clever software, there’s a programmer (and often a team of […]
Employee mobility is now the norm, with the proliferation of SaaS applications empowering the workforce to work on any device and from any location, whilst enabling […]
Business agility is mission-critical for financial services organisations. Market dynamics place a premium on the ability to adapt to changes such as M&A, add new locations […]
Manufacturing organisations face a variety of challenges when it comes to their IT environment. They need to be able to provide geographically dispersed R&D, plant floor […]
Over the past 18 months, organisations were forced to rapidly transform in order to maintain business continuity. However alongside this, cybercrime was also on the rise, […]
Whether operating from physical stores, e-commerce sites, or a mixture of both, retailers have faced many challenges over the last few months to continue generating sales, […]
We are delighted to announce that Ultima is now an accredited Living Wage Employer! This means that every member of staff working for us will earn […]
National Techies Day is celebrated on October 3rd. This day was founded by Techies.com and CNET back in 1998, to promote tech jobs and allow members […]
Techies Day was originally developed for the purpose of helping high school students become educated about careers in technology. It was first established in 1998 by […]
With over 22 billion records exposed to data breaches in 2020 (Tenable), ensuring a robust security policy has never been more important. The increase in cloud migrations […]
The term ‘Digital Transformation’ has become synonymous with large enterprise businesses and niche digital disruptors who are driving a paradigm shift within their industry group. However, organisations […]
With millions of employees working remotely and increasingly using home devices to connect to the corporate network, cyberattacks have increased exponentially over the past couple of […]
End User Computing (EUC) implementations have increased dramatically over the past 18 months, however the need for rapid deployment may have resulted in misalignment with your […]
In today’s rapidly evolving business world, keeping up with the pace of change is critical for continued business success – regular server refresh is now an […]
Automation is on everyone’s agenda at the moment, and this has only been amplified by the events of the past 18 months. As the impact of […]
Last week the Ultima ESG (environment, social & governance) team attended the COP26 climate conference, visiting the Green Zone. It was a tense final week as […]
Agile, scalable and flexible infrastructure is crucial in the current environment, enabling your business to respond quickly to fluctuating demand and market conditions. This requirement caused […]
Ultima have been made aware of a critical vulnerability which affects Log4j and is designated a 10 on the CVS vulnerability scale, the highest that a […]
We’ve been made aware of a critical vulnerability on the pkexec process that can be found in a large amount of major Linux distributions. This vulnerability has been […]
Welcome to the first in a series of blogs discussing the challenges of onboarding and offboarding employees from your organisation – otherwise affectionately known as JML […]
Talking to one my industry colleagues over a virtual beer during one of the lockdown phases, we got onto the subject of security; specifically, when you’re […]
Software supply chain attacks infamously made it to mainstream media back in December 2020 due to the now well-known SolarWinds attack which infected close to 18,000 […]
It’s interesting… I hear people say – isn’t gender diversity done? Haven’t we been doing this for a while now? Isn’t the problem solved? Unfortunately – […]
There are a whole host of workspace solutions out there for customers, but it’s well documented that Citrix and Microsoft have proved to be well-established leaders […]
Moving to the cloud seemed to promise so much – from longer-term savings to increases in efficiency and productivity. However, we’ve found that customers who migrate […]
Traditional onboarding solutions such as Identity and Access Management systems help us to manage our Joiners, Movers and Leavers using policies. These rely heavily on target […]
In today’s workforce environment, employees are widely distributed, as are their PCs. Making sure devices stay up and running is more critical and challenging than ever […]
We have seen two growing trends in 2022 – climate change and working from home. The move to flexible home-working reveals just how much electricity an […]
From the 8th to the 12th of March, SQL Bits held its annual data conference. SQL Bits is Europe’s biggest Microsoft data platform conference providing training and showcase […]
Microsoft SQL Server 2012 will go end of life in July 2022, meaning there is now less than a year to migrate or update existing legacy […]
Is there anything in the world more dull than Magnolia Paint…. The answer is yes, yes there is, Patching, yet it keeps many of us up […]
Application and cloud strategies are inextricably linked. IT organisations are modernising application portfolios to meet digital business needs. They’re also rethinking IT infrastructure to support the […]
In today’s digital age, cyber threats are constantly evolving and becoming more sophisticated. Traditional perimeter-based security approaches are no longer enough to protect your network from […]
Here at Ultima Labs, we are constantly striving for innovation to help our customers get the best value and services possible, especially when it comes to […]
As the proliferation of IoT devices increases and the threat landscape becomes increasingly complex, organisations need to re-evaluate their strategies. Although cybersecurity is top of many […]
Ultima – Scott Dodds, CEOFor over 30 years Ultima has built its business on the constant flow of innovation from our key technology partners. These so-called […]
At Ultima we recognise that innovation is vital in the workplace which is why we have named July as our Innovation Month for our internal communications […]

Join our virtual event 'Microsoft Monthly Webinar: Crucial Announcements and Updates with Ian Gerrard, Microsoft Licensing Consultant for the Ultima Group on Thursday 5th April 2023. There are […]
Vendor news
Ultima, the AI-powered cloud, security, and digital managed service provider, has today been awarded EMEA Partner of the Year by Kroll, a leading independent provider of […]
In this Issue: Changes to From SA Licenses The “From SA” discount from Microsoft, which facilitated the transition from on-premises software assurance to cloud subscriptions, has […]
Changes to From SA licences Microsoft have announced changes to the availability of From SA licences. Microsoft introduced this discounted sku in August 2014 as a […]
Cisco’s Identity Services Engine (ISE) and Network Access Control (NAC) are at the forefront of addressing these challenges, offering robust security solutions. This blog post will […]
In 2023 we witnessed the frequent use of native services in Public Cloud with little consideration shown to third-party services that provide more advantageous features at […]
As we venture deeper into the digital age, the Internet of Things (IoT) is reshaping our world. From smart homes to intelligent business operations, IoT devices […]
Microsoft first launched M365 Copilot in November 2023 with the intent to bring the power of generative AI to businesses of all sizes across every industry. […]
Microsoft CoPilot Microsoft has recently unveiled an exciting update in its repertoire with the renaming of Bing Chat Enterprise to the more streamlined “Co-Pilot.” This hotly […]
Microsoft M365 Copilot is a powerful tool designed to enhance productivity and streamline workflows. However, to truly unlock its potential, users need to have a solid […]
Copilot Essentials: The Business Case for Microsoft CopilotAs business leaders, none of us can ignore the change and potential power of AI to every aspect of […]
October is well underway and as Autumn approaches we once again found ourselves descending upon Barcelona for the Canalys Forums! This is an annual event during […]
Public Cloud adoption for many organisations has not been a smooth ride. Many decisions aimed at reducing complexity and cost have had the opposite effect often […]
Protecting Your Data in Today’s Corporate Landscape In today’s data-centric corporate landscape, safeguarding sensitive information is paramount, especially within the confines of your organisation. Picture a […]
Organisations today need to confront the ever-expanding challenge of managing their datacentre storage efficiently. For many, the problems of capacity constraints and the looming threat of […]
Microsoft is ushering in a new era of AI that promises to reshape our digital experiences. Last week they announced their vision for Microsoft Copilot at […]
Microsoft TSI TSI, which stands for Tech for Social Impact, represents a crucial initiative in the realm of technology. At the forefront of modern business and […]
Microsoft Teams changes in Europe After the EU probe into Microsoft’s practice of bundling Teams with Office 365 and just four or so weeks later, Microsoft […]
In today’s digital landscape, robust cybersecurity is no longer a luxury but a necessity for organisations across all industries. With cyber threats becoming more sophisticated and […]
Five months ago, Microsoft announced the launch of the very aptly named M365 “Copilot”, an AI-driven tool that leverages large language models (LLMs) to serve as […]
Register for our next Microsoft Webinar: Demystifying Microsoft Licensing – Navigating the Essentials for Business Success Join our monthly Microsoft Licensing webinar on September 13th hosted […]
Microsoft Inspire 2023 was held between July 17th to July 20th and these are the main updates from a Microsoft licensing, products and commercial stance. A […]
Register for our next Microsoft Webinar Join us in our upcoming Microsoft webinar with Ian Gerrard on July 12th at 10am – 11am to gain insights […]
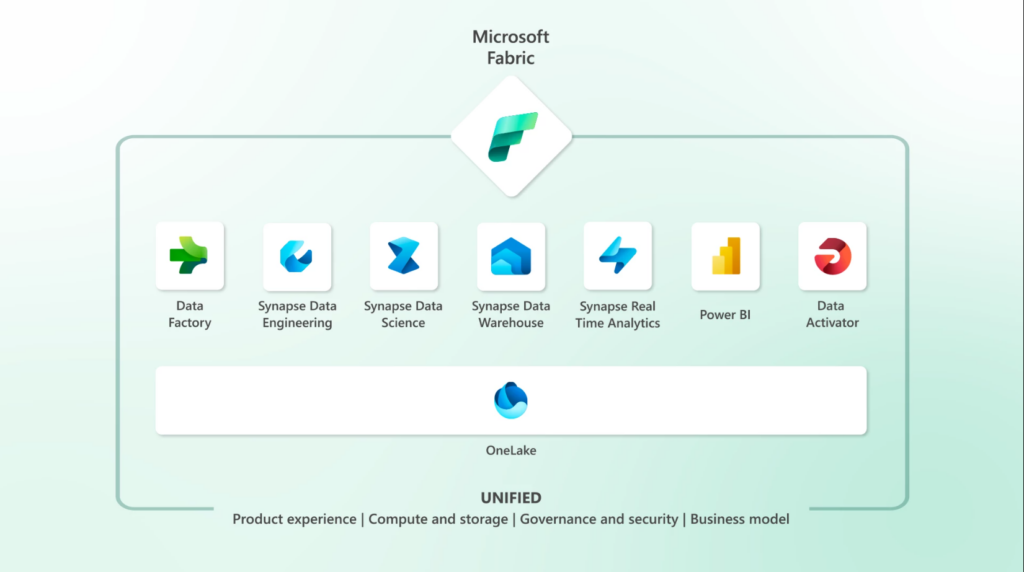
Last week, Microsoft announced Fabric, their new data and analytics platform. This is pitched as being a unified service bringing together multiple features and capabilities to […]
Register for our next Microsoft Webinar During our upcoming Microsoft webinar on June 14th at 11am-12pm with Ian Gerrard, you will have the opportunity to hear […]
As technology continues to advance and become an integral part of our lives, electronic waste (e-waste) has become a growing concern. E-waste is the accumulation of […]
Return of Ultima’s Microsoft Webinar Series! There are two large market influencers for Microsoft licensing customers currently, and they are impacting most decisions being made by […]
Reducing cybersecurity risk and ensuring data availability through secure backup is a priority to any organisation. NIST have defined a Security framework which guides customers in the […]
Citrix has announced an 8% price increase for all relevant Citrix products due to current inflation and rising costs. The price update will occur on April […]
InTune Suite Back in October 2022, Microsoft confirmed that InTune would become a wider suite and effectively a new ‘family’ of products. This has meant the […]
If, like me, you’ve been watching the rapid development of ChatGPT and wondering “what’s next”, Microsoft’s announcement of Co-Pilot last Thursday is a turning point in […]
Join our virtual event 'Microsoft Monthly Webinar: Crucial Announcements and Updates with Ian Gerrard, Microsoft Licensing Consultant for the Ultima Group on Thursday 5th April 2023. There are […]
The recent ransomware known as “VMware ESXiArgs” have been reported to be targeting out of date ESXi servers globally. The ransomware infects virtual machines, encrypting all of […]
Microsoft 365 Basic Microsoft announced that the OneDrive Standalone plan became Microsoft 365 Basic on 30 January, 2023 and includes the same 100GB of cloud storage […]
Price Changes on 1st April 2023 Microsoft confirmed a 9% price increase to impact cloud services on 1st April 2023. Please contact us to learn more […]
Microsoft 365 is constantly evolving and introducing new features to help businesses and individuals stay productive and connected. In this blog post, we’ll highlight some of […]
Dell Technologies Inc posted a 68 percent rise in quarterly operating profit last week, as demand for servers and network equipment softened the blow of weak PC […]
Organisations must start prioritising their credential theft protection. With most data breaches now linked to stolen credentials, this common and hard to detect threat, is further […]
Cisco has launched two new switches; Nexus 9232E and Cisco 8111. The Nexus-branded appliance runs Cisco’s in-house network operating system, while the latter is designed for […]
Security Defaults are being enabled by Microsoft for some existing customers. What does this mean for your business? In the summer of 2022, Microsoft announced the […]
Microsoft has announced that they are increasing their SQL Server Licenses by 10% from 1st January 2023. This follows the launch of the SQL Server 2022 […]
Hewlett Packard Enterprise’s GreenLake Cloud Services Commercial Business is being fully integrated into the core operations of the organisation. The HPE GreenLake platform continues to be […]
This year’s Microsoft Ignite was focused on how Microsoft Cloud is helping customers do more with less. The conference showcased the best of what’s next for […]
The challengeMicrosoft 365 cloud-delivered email has become core to more than two-thirds of the world’s email communications infrastructure. Despite native security and resilience capabilities included within […]
New changes for SQL Server High Availability and Disaster Recovery: Microsoft recently announced changes to the benefits available for organisations who purchase Software Assurance (SA) with […]
I’m going to open this blog with possibly the least original statement ever – we’re living in a time of immense change. Politics, economics, pandemics, sustainability, […]
General Availability of Teams Phone Mobile Microsoft announce the General Availability of Teams Phone Mobile, previously known as Operator Connect Mobile, which gives users a single, […]
The world we live in is vastly different from the start of 2020, both economically and socially. The challenges of the pandemic have been felt across […]
Last month, HPE brought together thousands of business leaders and technologists from across the globe to prepare for the next wave of digital transformation, powered by […]
Following a comprehensive audit process, we’re delighted to announce that we’ve been awarded the Microsoft Advanced Specialisation in Windows Server and SQL Server Migration (part of […]
On the 19th August 2021, Microsoft announced an update to their commercial pricing for Microsoft 365. This change will go into effect on 1st March 2022. […]
We’ve been made aware of a critical vulnerability which would allow an attacker to gain control of a PC via a user visiting a compromised site […]
Sheffield City Trust are a not-for-profit organisation who operate sport, leisure and entertainment venues on behalf of the council, ensuring these are affordable and accessible, and […]
An NSX-T network starts with a meshed network of dedicated appliance VMs, distributed in a redundant fashion across hypervisors in your data centre(s) and cloud-based VDCs […]
Read below for all the latest news and updates from Microsoft this month. Important Price Increases On 1st March 2022 Microsoft is due to implement the […]
At Ultima, we recognise the impact of transformative technologies and support making a positive societal impact and we are proud to demonstrate our commitment by signing […]
At this week’s Ignite conference, Microsoft released some key Azure Infrastructure announcements and in this blog, we look at the top 10 key takeaways: Azure Virtual […]
Through the Citrix Service Provider (CSP) model, Ultima can help deliver a cloud-enabled workspace that’s easy to deploy, infinitely scalable with Citrix Cloud, and available with […]
Read below for all the latest news and updates from Microsoft this month. Microsoft Price Increases Coming March 2022Starting 1st March 2022, Microsoft are increasing the […]
Read below for all the latest news and updates from Microsoft this month. Microsoft Price Increases Coming March 2022Starting 1st March 2022, Microsoft are increasing the […]
Read below for all the latest news and updates from Microsoft this month. Microsoft Price Increases Coming March 2022Starting 1st March 2022, Microsoft are increasing the […]
Read below for all the latest news and updates from Microsoft this month. Microsoft Price Changes From 1 March, 2022: • Office 365 El (up to […]
Citrix loves a re-brand. Fact. For those of you who have been down this road one or more (long live XenApp) times before, you might be […]
Read below for all the latest news and updates from Microsoft this month. Microsoft Defender for Business This is Microsoft Defender specifically for organisations under 300 […]
As a business that was founded on the back of selling memory some 32 years ago now, it’s fair to say we know a thing or […]
Ultima have been made aware about the Microsoft Zero-Day Vulnerability – Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability (CVE-2022-30190) CVE-2022-30190 – Security Update […]
Read below for all the latest news and updates from Microsoft this month. New Microsoft Teams Licensing On 1st September 2022, Microsoft retried Teams Room Standard […]
Read below for all the latest news and updates from Microsoft this month. New Product – VIVA Sales Microsoft are introducing Viva Sales, a new seller […]
Businesses are making great progress in becoming technologically advanced, with their focus turning to the “digital imperative”- that is, delivering integrated technology that helps them differentiate […]
As a business owner, you are always looking for ways to save money and reduce costs. One area where you may be able to save is […]
Having worked in the industry previously in a Cloud Marketing role, I recently joined Ultima as a new Cloud Success Specialist, following my desire to work in […]
Read below for all the latest news and updates from Microsoft this month. Windows 365 is Announced Microsoft has finally unveiled Windows 365, its new PC-as-a-service […]

International Women’s Day (IWD) is a global event celebrated annually on March 8th to recognise the social, economic, cultural, and political achievements of women. The day […]
Ultima news
Hello and welcome to my Microsoft licensing blog, where I share my insights and tips on Microsoft licensing for businesses. Today I want to talk about […]
Ultima, the AI-powered cloud, security, and digital managed service provider, has today been awarded EMEA Partner of the Year by Kroll, a leading independent provider of […]
While artificial intelligence (AI) has become even more prevalent with the rise of large language models and computer vision capabilities, the question that is often asked […]
Hi everyone! Chris here from the Ultima Labs team. We’re pleased to announce that we’ve hit a new major release milestone with our IA-Connect product for […]
Ultima, a new generation AI powered managed services provider across Cloud, Security and Digital Workspace has announced the establishment of a new office in South Africa. […]
Ultima, a new generation AI powered managed services provider across Cloud, Security and Digital Workspace announces the appointment of Andre Prins as Country Manager for Ultima, […]
Ultima, a recognised expert in cloud, security, digital workspace, data, and AI solutions and managed services, has been confirmed as an official supplier on all 8 […]
Let’s tackle the elephant in the room—money. Finances are a frequent topic of conversation, and the world of cyber security is no exception. As someone from […]
The “Joiners, Movers, and Leavers” (JML) process is an integral part of human resources and IT management in any organisation. Traditionally, the process was manual and […]
Businesses are not the only Targets… Over the last 12-18 months, many sectors of society, specifically the public sector have found themselves vulnerable to significant disruption […]
The ever-evolving technological landscape is posing significant challenges for UK organisations across various sectors, with the surging demand for IT talent driving an increasing reliance on […]
In today’s digital landscape, businesses rely heavily on IT systems across on-premises and the cloud; ensuring a robust disaster recovery strategy is paramount. Unforeseen events such […]
International Women’s Day (IWD) is a global event celebrated annually on March 8th to recognise the social, economic, cultural, and political achievements of women. The day […]
By nature, human error is normal. We’re not made to perform repetitive tasks at volume. On average, it’s usual to experience 10 to 30 errors per […]
At Ultima, we believe that good ethics are the foundation of good business. Unethical behaviour can severely damage the trust stakeholders place in an organisation and […]
Alongside generations of product experience held throughout our teams, we invest in our people so that they can continue to provide the latest advice, technical support, […]
Our Services We’re working with our customers to help them achieve their sustainability goals by reducing their reliance on physical services and transitioning them onto the […]
At Ultima, we see sustainability and humanity’s response to climate change as one of the greatest challenges of our lifetime. We must plan for a cleaner, […]
As Chief Financial Officer, I see the rise of Environmental, Social and Governance (ESG) reflecting changing attitudes that Ultima must consider. From how our actions affect […]
With the hybrid workforce and ‘working anywhere’ here to stay, coupled with an explosion in data growth, the daily demands upon an organisation’s infrastructure have never […]
September was Ultima’s volunteering month and with that we are excited to launch a new partnership with the Million Mile Clean. Suffers Against Sewage created their […]
At Ultima we are passionate about doing our part to support the community. This year we are delighted to be supporting Mind who provide advice and support to […]
Climate change is affecting our planet dramatically with CO2 in the atmosphere reaching record levels in May 2020, hitting 417 parts per million. The last time […]
To coincide with international friendship day, we take a look at the importance of building relationships in the workplace. People are social creatures by nature and […]
We are delighted to announce that we have been shortlisted for the 2021 SaaS Awards Program for the Best SaaS Newcomer. Now in its sixth year […]
At Ultima we are passionate about supporting early in careers and upskilling our workforce. Apprenticeship programmes are an important part of this, providing a learning structure […]
As part of Ultima’s Innovation Month throughout July, we were delighted to run our very first Hackathon. With innovation at the heart of our industry and […]
We’re delighted to announce that Ultima has been named as a finalist in the ‘Cloud Services Provider of the Year’ category at the CRN Channel Awards 2021 for the second […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
International Week of Happiness at Work (23rd – 27th September) is a new initiative originating from the Netherlands, which was created to encourage employers to make […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
At Ultima we are committed to doing our part to support the local community as well as the wider environment. To coincide with Make a Difference […]
100 Miles in October is a fundraising challenge for Mind. Participants could complete their miles however they liked – running, walking, or a bit of both! […]
Ultima are proud to be supporting STEM (science, technology, engineering, and mathematics) Day on 8th November. In a industry driven by rapidly changing technology, it’s more […]
We have entered the holiday season with a popular annual holiday upon us—Thanksgiving. Christmas songs try to say otherwise, but it just doesn’t get better than […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
2021… The year we have left behind us. What words immediately spring to mind when we think of 2021? For me – I’ll start with celebration […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
At Ultima we are commitment to supporting a positive work-life balanced for our employees so, like many other companies we moved to a hybrid way of […]
Ultima are proud to be supporting International Women’s Day on 8th March 2022. Creating a diverse workforce and encouraging women in technology is instrumental in driving […]
We’re proud to announce that we’ve just achieved Microsoft’s Azure Virtual Desktop Advanced Specialization partner status. This Advanced Specialization requires that partners exhibit “deep knowledge, extensive […]
Last year we were delighted to launch our High Impact Teams (HIT). These teams cover a variety of different topics and enable employees across the business […]
Preview Feature Announcements At the recent Ignite conference, Microsoft announced some new details for the upcoming release of SQL Server 2022. In a video with Microsoft’s Bob Ward, […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
Now more then ever poor mental health is on the rise. Despite some progress over the past years, there remains significant workplace stigma and bias […]
At Ultima we are passionate about supporting both the local community and those topics that are close to our employees’ hearts. This year we are delighted […]
This month is our wellbeing and mental health month in the Ultima Group. A theme which is so important and resonates to many of us. In […]
The business world is constantly talking about the importance of diversity and inclusion. But what does that actually mean? Diversity refers to the variety of people […]
Cloud, security and digital service provider, Ultima Business Solutions Limited, owned by Apse Capital Limited, has today acquired The AntiSocial Engineer Limited, an ethical social engineering company that helps […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
Every June, Pride Month is celebrated all around the world to celebrate LGBTQIA+ individuals and their accomplishments, (Lesbian, Gay, Bisexual, Trans, Queer/Questioning, Intersex, Asexual plus Allies). In honour […]
Microsoft Microsoft’s flagship annual event Inspire took place predominantly virtually again this year from 19th – 21st July and, as always, the updates came thick and fast! In […]
On Wednesday 6th July we are holding one of our quarterly events for all employees of Ultima Group. With lots of Team Ultima being hybrid or […]
We’re pleased to share with you the Ultima Partner Pulse, bringing together the latest updates from some of the key partners we work with. If you […]
A year ago, we were delighted to launch our partnership with Ecologi as part of our commitment to taking care of the environment through sustainable practices. […]
Privacy Policy | Terms | Modern Slavery Statement | Ethical Statement | Diversity and Inclusion | Sustainability | Cookies | Ultima Certifications | Commitment to Quality | Carbon Reduction Plan | Corporate Compliance Policy | Commitment to Security | Gender Pay Gap Report | Health and Safety Policy | ESG Policy | Ultima Labs EULA | Business Continuity Strategy | Environmental Management Policy
© 2022 Ultima Business Solutions Limited. All rights reserved. | Registered Address: Gainsborough House, Manor Farm Road, Reading, England, RG2 0NA | Company Registration 02521249 Registered in England & Wales